Petya in Tatarstan: virus turned computers at Kazancompressormash off
The ransomware sent HMS Group to stone age, but Kaspersky Laboratory is sure it is the fault of very admins
Petya is already in Kazan. The IT misfortune did not pass Kazancompressormash by – the factory has been copying with the encrypted virus for the third day. The work in the headquarters of HMS Group the enterprise belongs to also stuck. The hacking attack almost sent them to the stone age: instead of a request via e-mail, it is offered to use a traditional post, it is impossible to reach out to anybody inside the company because all phone numbers were saved on the computer. Curiously, victims of the cyber attack used products of one of the leading computer security laboratories. Realnoe Vremya tells the details.
Letter in envelope: ransomware virus sent enterprises to past century
Petya ransomware virus that attacked Ukrenergo, DTEK and Kyivenergo, Rosneft, Home Credit (over 80 enterprises in Russia, Ukraine and Europe in total) had no mercy on mechanical engineering from Kazan. Kazancompressormash can't recover its work for the third day due to the attack. The production was not affected. But the work of the office stuck. No computer runs. The situation became absurd – Realnoe Vremya could not get an official comment about the damage done by the virus to Kazancompressormash because the press service just can't receive a request. E-mail doesn't work, a secretary of the enterprise offered to send the letter via traditional post.
The ransomware virus also sent NIIturbokompressor AO to the past century. The secretary complained that the computers had not been working for ''several days already''. This is why they recalled that fax existed.
 ''We disconnected all electronic systems from power, now our engineers are checking the rate of the damage. If needed, they will work on the weekend to enable us to work on Monday,'' says Aleksandr Kharitonov, senior constructor at NIIturbokompressor AO.
''We disconnected all electronic systems from power, now our engineers are checking the rate of the damage. If needed, they will work on the weekend to enable us to work on Monday,'' says Aleksandr Kharitonov, senior constructor at NIIturbokompressor AO.
According to him, the virus attack did not paralyse the activity of the enterprise but stopped and complicated the work.
Petya reached phone notebook
Kazancompressormash and NIIturbokompressor became victims of the cyber attack together with other enterprises belonging to HMS Group AO – 18 organisations located in Russia, Belarus, Germany and Ukraine. The computers turned off on 27 June in the afternoon.
''HMS Group was partially affected by the global hacking attack. We continue to evaluate the situation and take all the necessary measures to minimise the above-mentioned negative impact,'' the company's official page says.
They could not find out the degree of the damage and other details of the attack for the same reason – computers don't work. Moreover, they could not connect Realnoe Vremya's reporter with a corresponding department or expert who could comment on the situation.
''I don't remember internal phone numbers,'' the company's secretary modestly replied. An offer to look for numbers was followed by a deep sigh and explanation that all the data is stored in the computer that doesn't work.
Kaspersky Lab: ''If this security model was turned off by administrators, there was an infection''
Realnoe Vremya managed to know the victims of Kazancompressormash and NIIturbokompressor took security measures, the enterprise used products of Kaspersky Lab. The laboratory notes that ''in the majority of cases, products of the Kaspersky Lab successfully and very quickly blocked the initial attacking vector of this encrypted viruses with System Watcher. But it seems that it did not manage to protect the users 100%.
 ''Modern anti-viruses are a complicated security system consisting of many components. When the virus appeared, a component responsible for blocking depending of programmes' behaviour caught it. If this security model was turned off by administrators, there was an infection. The situation is analogous when products have too old versions that simply don't have this component,'' Director of Kaspersky Lab Research Centre in Russia Yury Namestnikov commented Realnoe Vremya.
''Modern anti-viruses are a complicated security system consisting of many components. When the virus appeared, a component responsible for blocking depending of programmes' behaviour caught it. If this security model was turned off by administrators, there was an infection. The situation is analogous when products have too old versions that simply don't have this component,'' Director of Kaspersky Lab Research Centre in Russia Yury Namestnikov commented Realnoe Vremya.
By 28 June, Kaspersky Lab detected over 2,000 attacks. The company's blog post says that ''the ransomware uses a standard, solid encryption scheme so this appears unlikely unless a subtle implementation mistake has been made''. According to Kaspersky Lab, the bitcoin wallet of criminals received about 2,54 bitcoins, which is a bit less than $6,000, within a day as a result of 24 transactions.
The company advises to use a reliable anti-virus with an embedded anti-ransomware protection, update Microsoft Windows and all the third party software to not become a victim of cyber fraudsters. It is extremely important to apply the MS17-010 bulletin immediately, not to open attachments from untrusted sources, back up sensitive data to external storage and keep it offline.
Tatneft is ''alive'', victims did not go to the police
Earlier the media told that the virus attacked another Tatarstan enterprise – Tatneft. However, the company denied the information. The Tatarstan Ministry of Internal Affairs told Realnoe Vremya that it did not receive official complaints about Petya virtual ransomware from enterprises of the republic and citizens. Just in case, the police reminds what its victims should not do: don't pay in any case.
We should remind that Petya is spread through files attached to e-mails. The virus starts to encrypt the MBR of the boot sector. This record is the first sector on any hard disk, it contains a partition table and a loader that uses this table to retrieve the information about which part of the hard disk the system will boot from. The original MBR is stored in the 0x22 sector of the disk and is encrypted using the XOR byte operation with 0x07. As a result, the information on the computer's disk is substituted by the virus' data, according to experts of Positive Technologies.
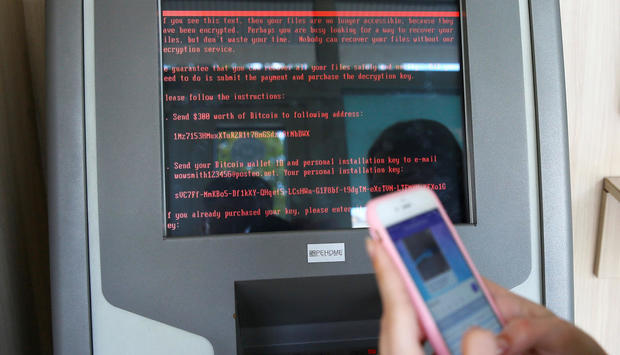
After the malicious file is opened, a task is created to restart the computer with a delay of 1-2 hours. If disks are successfully encrypted after the reboot, a window with a message about a $300 ransom to be paid to obtain the unlock key is displayed on the screen or pay in cryptocurrencies to get the key to unblock the files. By the way, the e-mail used by the criminals has already been banned, which makes money transaction useless.